Trending Now
How to Install Jenkins in Linux 7 | CentOS 7
Jenkins is an open source automation server or tools for continuous integration and continuous delivery (CI/CD) pipelines that are widely used in various sectors....
How to Install Jenkins in Linux 7 | CentOS 7
Jenkins is an open source automation server or tools for continuous integration and continuous delivery (CI/CD) pipelines that are widely used in various sectors....
NTP Server Client Configuration using Mikrotik Router and Linux OS
How to Configure Linux OS as NTP Client with NTP Server as Mikrotik Router:
https://www.youtube.com/watch?v=VtHMkPgV_VI
How to Setup a Complete Mail Server(Postfix) using SquirrelMail(Webmail) in CentOS...
A mail server is a server that handles and delivers e-mail over a network or internet. A mail server can receive e-mails from client...
YUM and FTP Server Configuration in RHEL 7 (Step by Step)
To show the mounted DVD or ISO image of RHEL-7.0.
# df -h
/dev/sr0 3.5G 3.5G 0 100% /run/media/root/RHEL-7.0 Server.x86_64
This command will enter the all rpm...
Q3: Managing Local Users and Groups | RHCSA Exam Questions and...
The Red Hat Certified System Administrator (RHCSA) exam is a leading and recognized certification that helps candidates increase, develop and incorporate administrative skills and...
Q2: Installing and Updating Software Packages | RHCSA Exam Questions and...
Today i will discuss question number two of Linux System Admin RHCSA EX200 Exam. This question usually asks to configure local yum repository with...
Malware in Adobe: The New Attack from BlackOasis
The Malware in Adobe has given much to talk about and since threats to computer security are the order of the day, today I bring...
Fake Movie Maker on Internet: Protect you from Hackers!
Fake Movie Maker appeared on internet, so hackers improve their tactics every day. That’s why they are using old programs to develop new scams....
Wi-Fi protection: Ways to protect Wi-Fi
Wi-Fi protection: Why is it so important? It is becoming a serious issue. Already there are several cases where multiple people have been hacked...
How to use Encrypted messages Gmail and why?
How to use encrypted messages Gmail?
Encrypted messages Gmail aren’t new, but if you want to improve your IT security, you should read this. Nowadays,...
Computer Virus: Most Famous Cyber Attacks in History!
The computer virus is becoming a more serious threat. Whether you prefer to call it Malware or virus, you must take into account a...
iPhone X – Top 5 Amazing Features
After months of speculations from the iPhone crazed users, Apple finally managed to release the much anticipated iPhone X. Apple however still managed to...
Top 20: Security Apps for Android you should have!
Security apps for Android are important. And we know that Android phones are a gem of technology, so you should take care of security...
OnePlus 5T: An alternative to iPhone X?
When talking about OnePlus 5T we have to remember that in recent years OnePlus has differentiated itself from its competition as the flagship killer,...
iPhone X Problems: Read this before buying new iPhone!
iPhone X phone was on the market the last weeks, and now some users are talking about some iPhone X problems. However, Apple is...
Samsung Galaxy S9: Features, price and…innovation?
Today, we bring very interesting about what, possibly, is the new Samsung Galaxy S9. After knowing when the mass production will begin and receive...
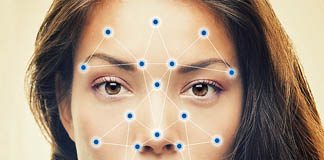
How to cheat iPhone X Face ID
Cheatings for iPhone X are on internet. And now the most important one is the process to trick the iPhone X Face ID, an...